How To Crack WPA/WPA2 With HashCat
Cloud-based service that attempts to recover passwords (hashes, WPA dumps, Office, PDF, iTunes Backup, Archives) obtained in a legal way (pentest, audit.). What kind of password? We support more than 90 hash algorithms: LM, NTLM, MD5, OSX, MySQL, Wordpress, Joomla, phpBB, Office, iTunes Backup, PDF, Archives, WPA (2). HashCracker is a python hash cracker which support hashing algorithms like SHA512, SHA256, SHA384, SHA1, MD5, SHA224. Ultimate Hashing and Anonymity toolkit. At md5hashing.net, you can hash (encrypt) any string into 66! Different hash types. As you probably know — the decryption of a 'hash' is impossible, but we offer reverse lookup (unhash; decryption) via our database (2000M records and counting).
The tutorial will illustrate how to install and configure HashCat on a Windows client and crack the captured PMKID or .hccap files using a wordlist dictionary attack.
'Hashcat is the self-proclaimed world's fastest password recovery tool. It had a proprietary code base until 2015, but is now released as free software. Versions are available for Linux, OS X, and Windows and can come in CPU-based or GPU-based variants.'
The WPA2 handshake can be captured on a Linux compatible client like Kali Linux with a supported WiFi card running on VirtualBox. Then converted to the right format depending on the captured method and moved over to the Windows client to be cracked.
Use the guides Capturing WPA2 and Capturing WPA2 PMKID to capture the WPA2 handshake. For this test we will use the famous 'Rockyou' wordlist.
DISCLAIMER: This software/tutorial is for educational purposes only. It should not be used for illegal activity. The author is not responsible for its use or the users action.
Step 1: Download HashCat
Hashcat do not require any installation, it is a portable program it requires you to unpack the downloaded archive.
- First you need to download Hashcat binaries from https://hashcat.net/hashcat/
- Navigate to the location where you saved the downloaded file, and unzip the file
Step 2: Download Wordlist
They are numerous wordlists out on the web, for this test we are going to use the famous 'rockyou'.
- Open the hashcat folder on your harddrive and create a new folder called 'wordlist'
- Download therockyou.txt wordlist from this Link.
- Save the downloaded file in the new folder'wordlist'
Step 3: Prepare Your Captured WPA2 Handshake
Depending on the method you used to capture the handshake you either must format the cap file to 2500 hash-mode or the PMKID file to hashcat 16800 hash-mode .
For how to format the files please see the guides Capturing WPA2 and Capturing WPA2 PMKID.
In this lab we are using a captured PMKID and a pcpa handshake formatted to hashcat readable format. 'HonnyP01.hccapx ' and ' HonnyP02.16800″.
I'm using two different home routers from D-Link and Technicolor for this experiment, both WiFi routers are owed by me.
- The 'HonnyP01.hccapx' file is captured from the D-Link router.
- The ' HonnyP02.16800″ file is captured from the Technicolor router.
Step 4: Start Hashcat
You need to run hashcat in CMD or PowerShell. In this example we will use CMD to execute our commands and crack the handshake.
Open CMD and navigate to the hashcat folder.
Type hashcat64 -h to display all options
Step 5: Crack WPA2
In the First example we will illustrate how to get the password from a converted pcap file '.hccapx'.
Copy your converted file to the hashcat folder, in this example i am copying the file HonnyP01.hccapx to my hashcat folder.
Next we will start hashcat and use the wordlist rockyou, type in the parameters below in CMD.

- hashcat64 the binary
- -m 2500 the format type
- -w 3 workload-profile 3
- HonnyP01.hccapx the formatted file
- 'wordlistrockyou.txt' the path to the wordlist
Hashcat will start processing the file, if you are successful the terminal will display the hash and the password.
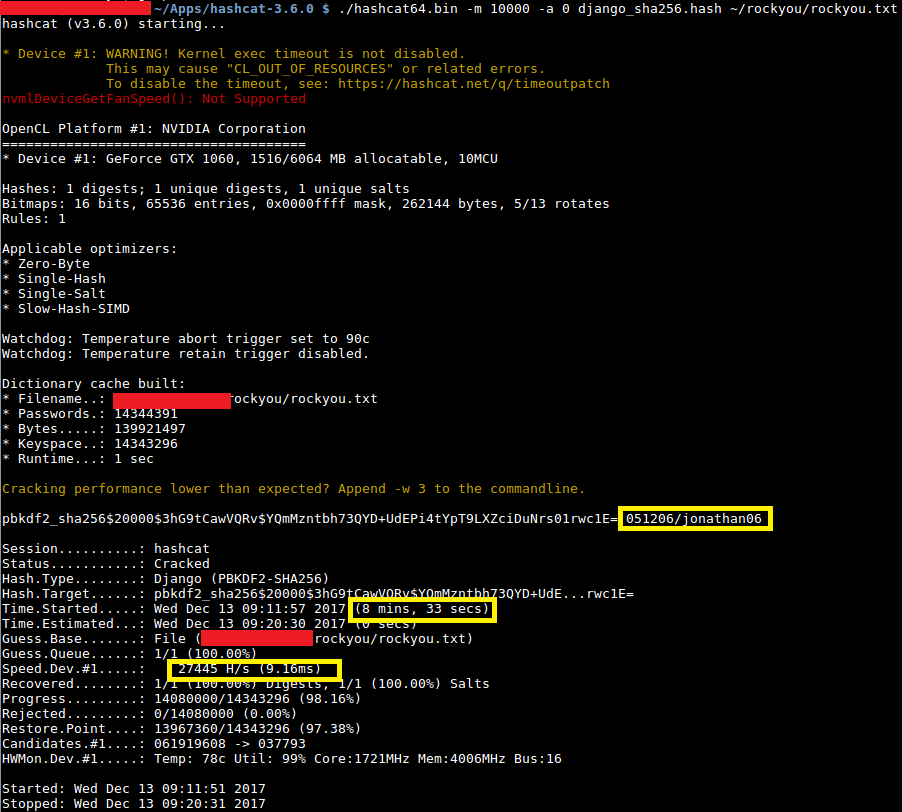
Here we can see that hashcat was able to match the hash to a password in the wordlist, in this lab the password to the D-Link WiFi is 'password'. You can chose to let the application run trough the wordlist or press 'q' to quit.
You can display the cracked password with the 'show' command or by running the same command again, all cracked hashes will be stored in the 'hashcat.potfile' in the hashcat folder.
To display the cracked password in CDM type the command bellow.
In the next example we will run the same command except now we use the 16800 mode to run the dictionary attack against formatted PMKID file captured from the Technicolor router.
- hashcat64 the binary
- -m 16800 the format type
- -w 3 workload-profile 3
- HonnyP02.16800 the formatted file
- 'wordlistrockyou.txt' the path to the wordlist

Here we can see that the cracked password is 'adsladsl' for the Technicolor router.
Extra: Brute Force Attack And Rule based attack
You can let hashcat brute force the file with the command bellow.
Or use ruled base attack.
Conclusion

- hashcat64 the binary
- -m 2500 the format type
- -w 3 workload-profile 3
- HonnyP01.hccapx the formatted file
- 'wordlistrockyou.txt' the path to the wordlist
Hashcat will start processing the file, if you are successful the terminal will display the hash and the password.
Here we can see that hashcat was able to match the hash to a password in the wordlist, in this lab the password to the D-Link WiFi is 'password'. You can chose to let the application run trough the wordlist or press 'q' to quit.
You can display the cracked password with the 'show' command or by running the same command again, all cracked hashes will be stored in the 'hashcat.potfile' in the hashcat folder.
To display the cracked password in CDM type the command bellow.
In the next example we will run the same command except now we use the 16800 mode to run the dictionary attack against formatted PMKID file captured from the Technicolor router.
- hashcat64 the binary
- -m 16800 the format type
- -w 3 workload-profile 3
- HonnyP02.16800 the formatted file
- 'wordlistrockyou.txt' the path to the wordlist
Here we can see that the cracked password is 'adsladsl' for the Technicolor router.
Extra: Brute Force Attack And Rule based attack
You can let hashcat brute force the file with the command bellow.
Or use ruled base attack.
Conclusion
Your home or office WiFi can be hacked if you are using a weak password, as always a strong and complex password is still the best defense against an attacker.
DISCLAIMER: This software/tutorial is for educational purposes only. It should not be used for illegal activity. The author is not responsible for its use or the users action.
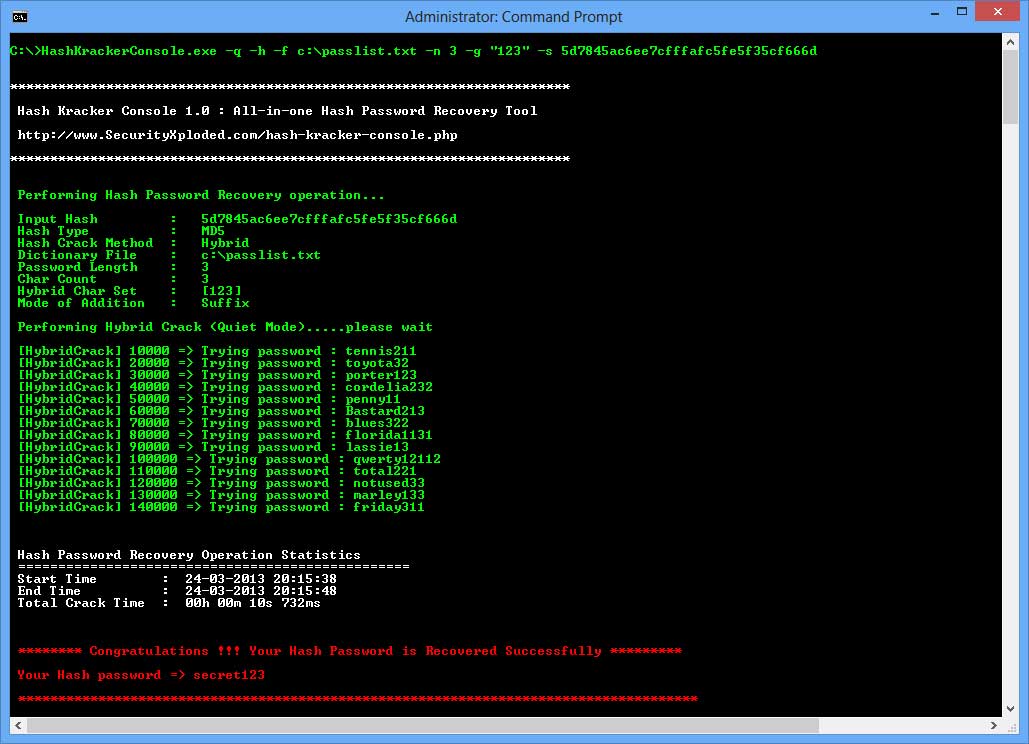
Supported hashing algorithms: SHA512, SHA256, SHA384, SHA1, MD5
Features: auto detection of hashing algorithm based on length (not recommended), bruteforce, password list
Arguments:
Hash Cracker Apk
type: hash algorithm (must be one of the supported hashing algorithms mentioned above or AUTO if you want to use automatic algorithm detection)
hash: can be either the hashed password, or a text file containing a list of hashes to crack (hashlist must be activated if hash is a text file containing multiple hashes)
mode: list or bruteforce
pwlist: list of passwords to compare against a single hash or a list of hashes
range:bruteforce string length range (default: 8-11)
hashlist: no parameters required for this argument, if hashlist is used, then hash should be a text file with more than 1 hash
chars: string of characters to pick from to generate random strings for bruteforce (default value is: abcdefghijklmnopqrstuvwxyzABCDEFGHJIKLMNOPQRSTUVWXYZ0123456789)
Examples:
Cracking a single hash with a password list:
hashcracker.py SHA256 11a1162b984fef626ecc27c659a8b0eead5248ca867a6a87bea72f8a8706109d -mode list -pwlist passwordlist.txt
Cracking a single hash with bruteforce:
hashcracker.py SHA256 11a1162b984fef626ecc27c659a8b0eead5248ca867a6a87bea72f8a8706109d -mode bruteforce -range 6 11 -chars abcdefghijklmnopqrstuvwxyz0123456789$#@
Cracking a list of hashes with a password list:
hashcracker.py MD5 list_of_hashes.txt -mode list -pwlist passwordlist.txt -hashlist
Cracking a list of hashes with bruteforce:
hashcracker.py MD5 list_of_hashes.txt -mode bruteforce -hashlist -range 6 11 -chars ABCDEFGHJIKLMNOPQRSTUVWXYZ0123456789
Salted Hash Cracker
Credits : kitploit.com
Nt Hash Cracker
CyberSecurity : un5t48l3.com
